The Messy Reality: Taming Your AI Strategy's Shadow & Sprawl
AI integration often introduces significant challenges: Shadow AI poses data security risks from unapproved tool usage, while pipeline sprawl creates operational headaches with complex ETL processes. Architectural strategies like in-platform model deployments, monitored gateways, and moving to single foundation models with on-the-fly data queries can simplify governance and reduce maintenance burdens. Consolidating data into a unified warehouse further enhances control, despite potential performance trade-offs for online services.

The AI revolution is here, and every company is scrambling to integrate it. The mandate from leadership is clear: go AI-first. While the promise of generative AI and machine learning is immense, the reality on the ground for developers and engineering leaders is often far messier. We’re not just talking about model accuracy; we’re grappling with critical issues like data security risks from "Shadow AI" and the operational nightmare of "pipeline sprawl." Let’s dive into the messy truth and explore architectural strategies to bring order to the AI chaos.
The Peril of Shadow AI
As AI adoption grows, 'Shadow AI' has emerged as a major security challenge. This refers to employees using unapproved, third-party AI services, often outside IT's control. The primary risk is data egress: sensitive company data (PII) or confidential information inadvertently sent to external LLM providers or unvetted AI tools. Imagine a sales team using an unsanctioned LLM for client proposals, or integrating AI with CRM without proper security. This dramatically expands your data's supply chain and attack surface.
To mitigate this, organizations are adopting architectural governance:
- In-Platform Deployments: Deploying AI models directly within approved data platforms (e.g., Snowflake’s Snowpark Container Services) ensures data and models stay within the established security perimeter of the approved data warehouse.
- VPC Deployments: For custom services, using your company's Virtual Private Cloud provides a secure, isolated environment.
- Monitored Gateways: Routing all AI-related API calls through a central gateway enables IT to monitor traffic, detecting and blocking sensitive data egress. AI can even assist in identifying these patterns.
- Controlled Data Access: Implementing granular access controls means specific AI systems, for instance in FinTech or healthcare, only access necessary electronic health record (EHR) data, with telemetry monitoring all data flow. This ensures models interact solely with approved datasets.
Taming the Pipeline Sprawl Monster
Beyond security, traditional machine learning setups suffer from 'pipeline sprawl.' Predictive AI models (e.g., for recommendations, fraud detection) commonly rely on numerous ETL pipelines for feature engineering. These pipelines aggregate data, like 30-day click activity, before feeding into models.
This creates a brittle, high-maintenance architecture. Debugging is a nightmare when an upstream pipeline fails, impacting multiple downstream models. Tracing data lineage through complex dependencies, as seen at LinkedIn, is incredibly time-consuming, and 'bit rot' makes maintenance a Herculean task.
To combat this, Kumo.ai champions a simplified model architecture:
- Single Foundation Model: Leverage one core model instead of many specialized ones.
- On-the-Fly Database Queries: Rather than pre-processing via ETL, the system queries the database at inference time. Using in-context learning, relevant data is fetched directly for a specific use case, then sent to the foundation model for a real-time response.
This shifts from static, pre-computed data flows to dynamic, real-time database lookups. The maintenance burden drastically shrinks, focusing on one core model and an online database interaction service, rather than an intricate web of ETL jobs.
The Case for a Unified Data Layer
For both Shadow AI and pipeline sprawl, a unified data warehouse layer offers significant benefits. Consolidating data for AI and analytics into a single warehouse simplifies governance, providing a central catalog to control dataset availability and access. This centralized approach enables consistent monitoring, directly mitigating Shadow AI risks.
However, a single warehouse isn't always ideal due to differing performance needs. Online services, such as e-commerce recommendations, require low-latency responses a typical data warehouse might not deliver. While analytics platforms have mature governance, online application backends often defer these considerations until scaling necessitates change.
Practical Takeaways
- Audit Your AI Footprint: Actively identify and track all AI tools used across your organization, approved or otherwise.
- Prioritize Data Governance: Implement robust strategies for data access control and egress monitoring, especially when integrating with third-party AI services.
- Architect for Simplicity: Evaluate your current AI pipeline complexity. Explore approaches that reduce the number of discrete data pipelines, perhaps through more dynamic data retrieval at inference time with foundational models.
- Consolidate Data Where Possible: Strive for a unified data warehouse for AI and analytics to centralize governance and simplify data access management.
FAQ
Q: What is Shadow AI and why is it a concern for developers? A: Shadow AI is the use of unapproved AI tools by employees, posing significant data security risks. For developers, this means sensitive company data (e.g., PII) could be exposed to external AI providers without vetting, creating compliance issues and expanding the attack surface.
Q: How does the single foundation model approach tackle pipeline sprawl? A: Instead of numerous ETL pipelines for pre-computed features, a single foundation model queries the database on-the-fly for context-specific data at inference time. This dynamic retrieval eliminates static pipelines, drastically simplifying data architecture, reducing maintenance, and easing debugging.
Q: What are the trade-offs of using a unified data warehouse for both AI and online services? A: A unified data warehouse simplifies governance and data access control for AI/analytics. However, it often can't meet the low-latency needs of online transactional services. Organizations may need separate online data stores, balancing centralized governance with application-specific performance.
Related articles
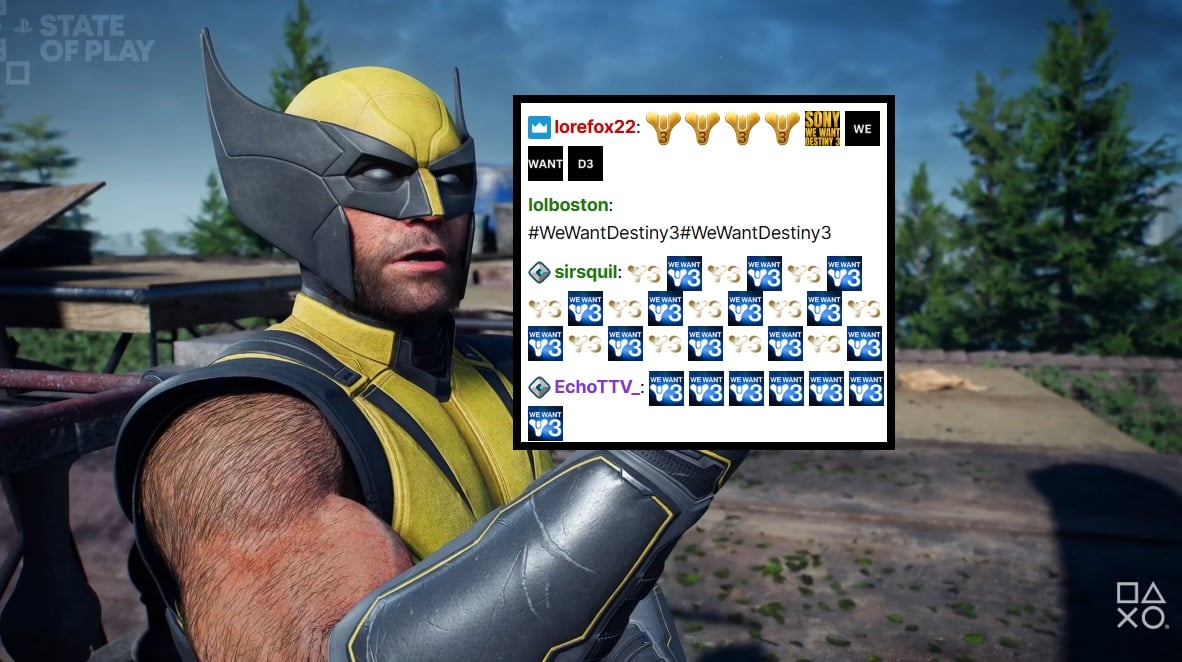
PlayStation Showcase Chat Swamped by Demands for Destiny 3
PlayStation's recent State of Play showcase was largely overshadowed by an impassioned fan campaign in the Twitch chat, demanding 'Destiny 3'. Amidst reveals for new PS5 games, the chat was relentlessly spammed with #WeWantDestiny3, fueled by the unexpected sunsetting of Destiny 2 and the reported absence of a direct sequel. This digital protest reflects widespread community frustration, amplified by a popular streamer and a petition with over 330,000 signatures.
Microsoft Unveils ASSERT, Simplifying AI Behavior Testing with Text
Microsoft has launched ASSERT, an open-source framework designed to simplify AI behavior testing. It enables developers to create comprehensive, application-specific evaluations using natural language descriptions, ensuring AI systems act as intended for particular products and services. The tool translates high-level goals into structured tests, generates scenarios, scores results, and logs execution paths.
Trump Orders Voluntary AI Model Review Before Release
President Trump has signed an executive order creating a voluntary framework for AI companies to share advanced models with the federal government before release. This initiative aims to bolster secure innovation and protect critical infrastructure, reflecting a shift from the administration's previous hands-off approach to AI safety. Companies opting for pre-release review may receive confidentiality protections.
Quick Share Meets AirDrop: A Welcome Cross-Platform Step
Quick Verdict: A Much-Anticipated Bridge For years, seamless file sharing between Android and iOS devices has been a frustrating chasm, often requiring clunky workarounds or third-party apps. This month, Google is
Blue Origin's New Glenn Explosion: Key Components Survive, 2026
Blue Origin announced that critical fuel tanks and key launch pad components survived last week's New Glenn rocket explosion, paving a faster path back to flight. CEO Dave Limp pledges a return to orbital missions before year-end, which is crucial for NASA's Artemis lunar program to maintain its tight schedule for crewed landings.
ZeroDrift raises $10M to protect AI models from themselves: AI
ZeroDrift, an AI compliance startup, has secured $10 million in seed funding from investors like a16z Speedrun. The company's service acts as a crucial intermediary, detecting compliance violations in AI-generated messages and rewriting them to meet regulatory standards like SOC 2 and GDPR. This rapid, oversubscribed funding round highlights the urgent demand for robust AI governance solutions as businesses scale AI adoption.